drspod 1 day ago • 100%
Not my post btw, just sharing the link :)
drspod 1 day ago • 100%
Sorry for the reddit link, I don't know of a mirror. This was posted just today, running on an EeePC:
drspod 1 day ago • 100%
drspod 1 day ago • 100%
The binaries in question are various GNU and FOSS tools from elsewhere, not part of the Ventoy project itself. So no, the Ventoy author does not own the copyright of the tools in question.
drspod 1 day ago • 87%
So your approach to security is that you cross your fingers and hope?
drspod 1 day ago • 100%
Ventoy has a lot of work to do if they want to earn our trust:
Remove BLOBs from the source tree #2795
This ticket has been open now for 5 months with no engagement from the maintainer.
Your install media and anything that modifies your EFI partition or UEFI firmware settings needs to be the most trusted part of your system. And here is Ventoy, a tool that looks open source and then includes a large number of binary blobs in its repository, with no indication of how they were compiled. This is horrible security practice and for me that's enough for me to never use it.
You can also see a discussion on the subject on HN here: https://news.ycombinator.com/item?id=40689629
A much better alternative, if you want a multi-boot USB, is GLIM: https://github.com/thias/glim
It's just a collection of Grub configs, so very simple and easy to audit.
drspod 1 day ago • 100%
From my understanding, a lot of code in the graphics drivers is special-case handling for specific games to optimize for the way that the game uses the APIs. Is this correct?
In which case it would make sense to have the game-specific code loaded dynamically when that game is launched, since 99.99% of the game specific code will be for games that the user never runs.
drspod 1 day ago • 100%
You can't improve on perfection.
drspod 2 days ago • 100%
I used Ubuntu from version 8.04 to 18.04 and not once did I have a successful upgrade between major versions. There is always something that gets broken to the point that a reinstall is necessary.
drspod 2 days ago • 100%
That's a huge difference, the estimate became 10,000 times smaller.
drspod 3 days ago • 100%
drspod 3 days ago • 100%
they can’t be jammed the way radio can.
I wonder how well these satellite laser links do with various types of cloud cover.
drspod 3 days ago • 61%
By repeating their rhetoric, even as a joke, it's just giving oxygen to people who don't deserve any form of publicity whatsoever. It would be better not to reference these batshit-insane conspiracy theories and then perhaps they would die more quickly.
This story is about French/space/communications/technology. Not American/politics/racist/conspiracy. Not one genre overlap, so there's no reason to even bring it up here. Maybe leave these jokes to the American politics threads.
drspod 3 days ago • 86%
(Federated) email didn't survive. It got completely subsumed by the major providers who now have control over everything email related. It's now impossible to run your own email server since none of the major providers will deliver your email without your mail server having first built a reputation.
The fediverse analogy would be if 99.9999% of users were on Threads and you couldn't interact with any of those users from any of the small independent fediverse servers. Frankly, that's exactly what it looks like is happening.
drspod 4 days ago • 100%
Wait until you see the ones that let you choose between "Accept All" and "Subscribe to monthly plan 4.99/mo"
I saw a website like that the other week and it was based in an EU country.
drspod 6 days ago • 100%
Got a link to that?
drspod 6 days ago • 78%
Can't wait to read about it telling someone to put glue on pizza.
drspod 7 days ago • 100%
It's not reading the contents of RAM via EM emanations, it's using the EM emanations caused by certain memory access patterns as a side channel to exfiltrate data. Of course, that data could be anything, including whatever is in RAM, but the point is that you need to be running the code that generates the necessary memory access patterns to transmit the bits of data. This is not like TEMPEST where you can reconstruct a video display just using the emanations.
drspod 1 week ago • 100%
Thanks! I was racking my brain trying to think of where I knew it from, and after seeing the page that you linked I'm almost certain that it's After Burner that is causing my brain to trigger the 80s association.
drspod 1 week ago • 100%
You can tell just from the font that this book is from the 80s
drspod 1 week ago • 99%
She's a great chess player but she's never been a World Champion. There's no need to embelish her story. She's currently training to become a surgeon at University of Missouri School of Medicine.
drspod 1 week ago • 100%
Is there something significant about this release, or are we just going to have a post every time every piece of software releases a new version?
drspod 1 week ago • 100%
perhaps
drspod 2 weeks ago • 100%
If it was plausible this would be bigger news. There's a claim like this every couple of months and none have held up to scrutiny so far.
> Threat actors are utilizing an attack called "Revival Hijack," where they register new PyPi projects using the names of previously deleted packages to conduct supply chain attacks. > > The technique "could be used to hijack 22K existing PyPI packages and subsequently lead to hundreds of thousands of malicious package downloads," the researchers say. If you ever install python software or libraries using `pip install` then you need to be aware of this. Since PyPI is allowing re-use of project names when a project is deleted, any python project that isn't being actively maintained could potentially have fallen victim to this issue, if it happened to depend on a package that was later deleted by its author. This means installing legacy python code is no longer safe. You will need to check every single dependency manually to verify that it is safe. Hopefully, actively maintained projects will notice if this happens to them, but it still isn't guaranteed. This makes me feel very uneasy installing software from PyPI, and it's not the first time this repository has been used for distributing malicious packages. It feels completely insane to me that a software repository would allow re-use of names of deleted projects - there is so much that can go wrong with this, and very little reason to justify allowing it.
drspod 2 weeks ago • 100%
I love that the local translation feature is getting regular small updates to make it more useable. It's a great feature.
drspod 2 weeks ago • 100%
Porges believes
This is an interesting article and yet you've chosen to quote the most speculative unscientific part of it from the final paragraph.
"Have you tried going outside" is not a scientific cure for depression.
drspod 2 weeks ago • 100%
7
drspod 3 weeks ago • 100%
Note to readers: Don't install python dependencies for random python projects of unknown provenance. PyPI is regularly being used as a vector for distributing malware. See recent news stories here: https://www.bleepingcomputer.com/tag/pypi/
You should manually check every package listed in requirements.txt and verify that it is a trustworthy python library.
drspod 3 weeks ago • 50%
Sorry but your satire isn't funny enough for me to continue reading when the page gets gradually darker as I scroll down so that it can show me a popup asking me to subscribe to your newsletter or whatever the fuck.
drspod 3 weeks ago • 100%
AI is definitely capable of making great music right now.
Got any links?
drspod 3 weeks ago • 100%
- Does your phone automatically join open wifi networks?
- Do you have worse cell signal than usual in this store?
drspod 3 weeks ago • 100%
But website ads don’t get the ad money like YouTube.
Their website doesn't even have ads
drspod 3 weeks ago • 100%
You can see the planned specs for the two different models on their indiegogo page: https://www.indiegogo.com/projects/emudeck-machines-retro-emulation-console-pc#/
I'm guessing they have a pre-selected all-in-one board (designed for mobile devices) and they're just designing a chassis around it. There's still a lot that could go wrong, but it's a bit more achievable than actually designing, testing and assembling your own board.
drspod 3 weeks ago • 100%
drspod 3 weeks ago • 100%
You need to find a schematic for your car's electronics in order to get a proper solution for what you're trying to do. I would be particularly cautious about connecting a relay coil to some unknown wiring. The back e.m.f. from a discharging relay coil could easily fry a microcontroller if it happens to be connected to one.
drspod 3 weeks ago • 100%
Slightly OT, but for these instructions that do pick range of bits, add, insert into range, does x86 have dedicated silicon in the ALU to implement this process or is it implemented in microcode? If it's the latter then how can it be faster than the equivalent unrolled instructions on a RISC ISA?
This is more of a general question about how microcode can be faster than using separate instructions, which is something I have never quite understood. Any CPU engineers that can enlighten me?
drspod 3 weeks ago • 100%
So that would make it 1.4m in the last two weeks which makes a big difference.
It would have been nice for the article to actually discuss these specifics. I'm not sure what we're supposed to take away from it.
drspod 3 weeks ago • 100%
He doesn't actually do the calculation required to give an estimate of what that number is.
Going on the stats in the article:
- assuming that Wukong has just surpassed the revenue of Steam Deck in the chart so we can treat their revenues as equal
- assuming Wukong price is $49.99 and average Steam Deck price is $500
- using the stat that 14m copies of Wukong sold on Steam so far
that would imply ~1.4m Steam Decks sold
The article does go on to say:
Keep in mind that by November last year, Valve said the Steam Deck had already sold "multiple millions".
So really this (very rough estimate) is telling us nothing that we didn't know already. The top seller charts are showing exactly what we would have expected to see.
 www.youtube.com
www.youtube.com
Description: "Featured is a playthrough of a blitz chess game between Rodrigo Vasquez and Vladimir Kramnik from an Early Titled Tuesday event which was held on October 17th, 2023. Kramnik recently admitted, via a YouTube comment on this topic of fair play surrounding him, that he played several tournaments under someone else’s chess\.com account. This act violates chess\.com’s Fair Play Policy. Kramnik played under Denis Khismatullin’s account, “Krakozia”. I share reasons why this is a violation of fair play policy, how a player can be negatively impacted because of it, and provide Kramnik’s YouTube comments where he attempts to explain it all."
 www.bleepingcomputer.com
www.bleepingcomputer.com
cross-posted from: https://lemmy.ml/post/4912712 > Most people know at this point that when searching for a popular software package to download, you should be very careful to avoid clicking on any of the search ads that appear, as this has become an extremely common vector for distributing malware to unsuspecting users. > > If you thought that you could identify these malicious ads by checking the URL below the ad to see if it directs to the legitimate site, think again! Malware advertisers have found a way to use Google's Ad platform to fake the URL shown with the ad to make it appear like a legitimate ad for the product when in fact, clicking the ad will redirect to an attacker controlled site serving malware. > > Don't click on search ads or, even better, use an ad-blocker so that you never see them in the first place! > > 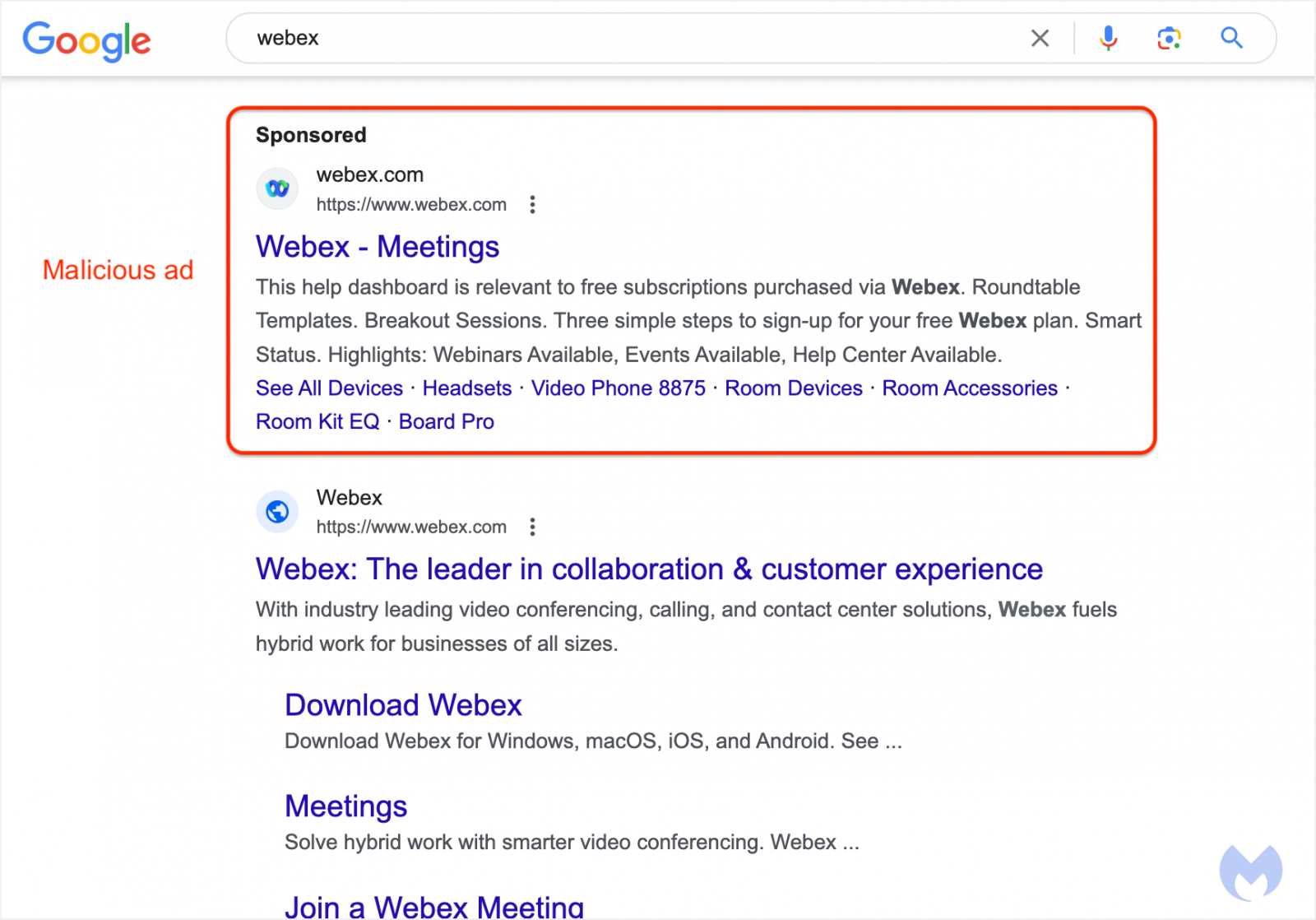
 www.bleepingcomputer.com
www.bleepingcomputer.com
Most people know at this point that when searching for a popular software package to download, you should be very careful to avoid clicking on any of the search ads that appear, as this has become an extremely common vector for distributing malware to unsuspecting users. If you thought that you could identify these malicious ads by checking the URL below the ad to see if it directs to the legitimate site, think again! Malware advertisers have found a way to use Google's Ad platform to fake the URL shown with the ad to make it appear like a legitimate ad for the product when in fact, clicking the ad will redirect to an attacker controlled site serving malware. Don't click on search ads or, even better, use an ad-blocker so that you never see them in the first place! 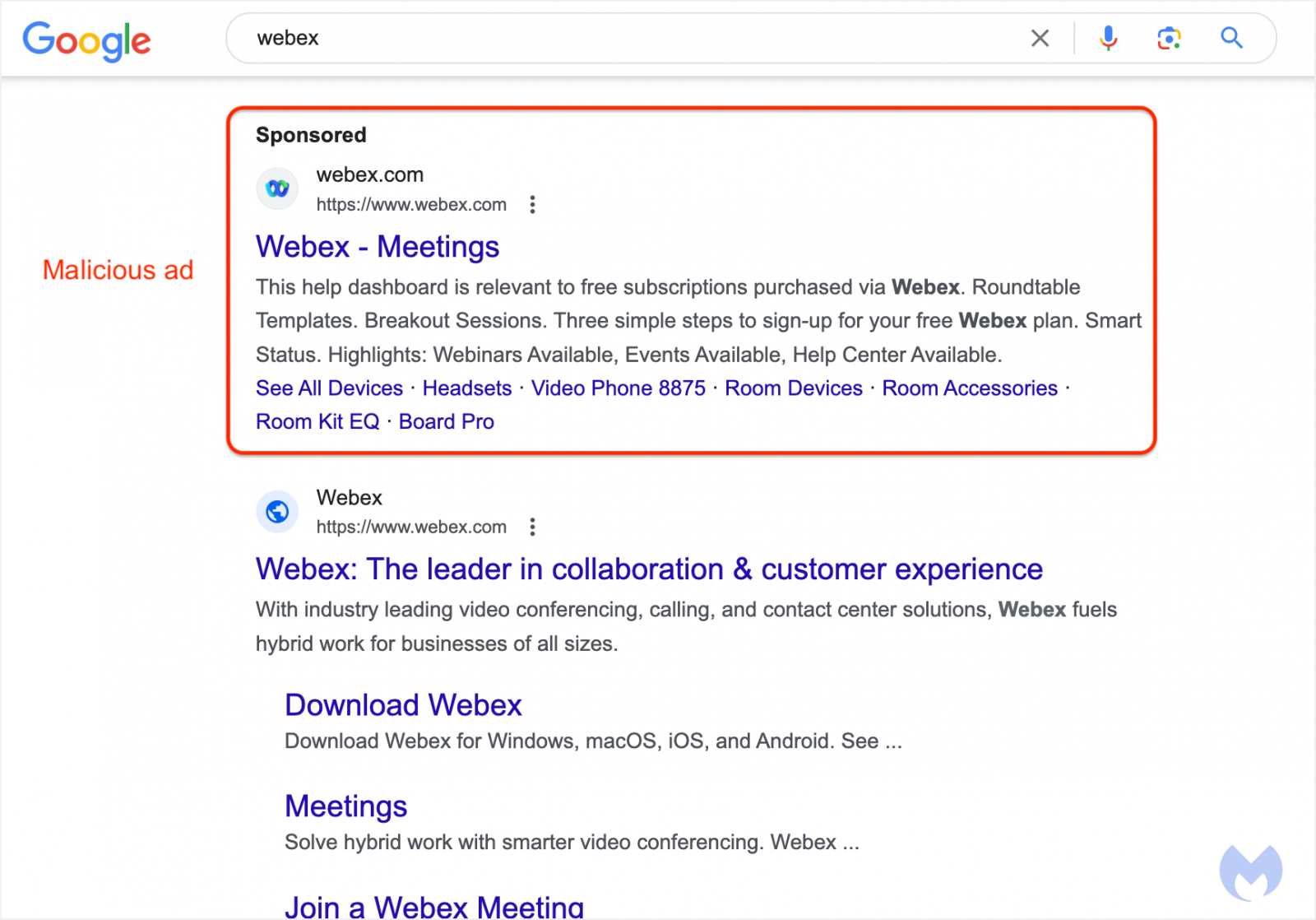
 www.bleepingcomputer.com
www.bleepingcomputer.com
A reported Free Download Manager supply chain attack redirected Linux users to a malicious Debian package repository that installed information-stealing malware. The malware used in this campaign establishes a reverse shell to a C2 server and installs a Bash stealer that collects user data and account credentials. Kaspersky discovered the potential supply chain compromise case while investigating suspicious domains, finding that the campaign has been underway for over three years.
**[SOLVED]: The issue was caused by having "Show read posts" unticked in Settings. This will hide your own posts from you!** I recently made a post^[1]^ to this community about a bug that I experienced and reported. The post does not appear in the `New` feed for /c/lemmy_support nor does it appear in my user profile under `Posts` ^[2]^. However the post does have 3 replies (from users on multiple different instances) which means that other users can see it across the fediverse, so it's not a federation issue. (Also, my account and the community are both hosted on the same instance - lemmy.ml). I was not subscribed to /c/lemmy_support at the time I made that post, but I am subscribed now to see if that affects my visibility of this post. Is this a bug, or am I misunderstanding how lemmy works? Interestingly, if I view my profile while logged out, it does show the posts that I made, but when logged in it shows zero posts in my profile. [1] https://lemmy.ml/post/1394597 [2] 
 github.com
github.com
See the images attached to the linked bug report. Where it usually says my username in the top-right, another user's name appeared. This happened twice in the last two days. I submitted the bug to the lemmy-ui project, but I'm not certain if this is a lemmy-ui problem, or a problem with the specific infrastructure setup of lemmy.ml, or even a backend issue. Any advice on whether I should post this bug report to somewhere else for greater visibility would be welcome. This could be indicative of a fairly serious security issue (or it could be a completely cosmetic bug).